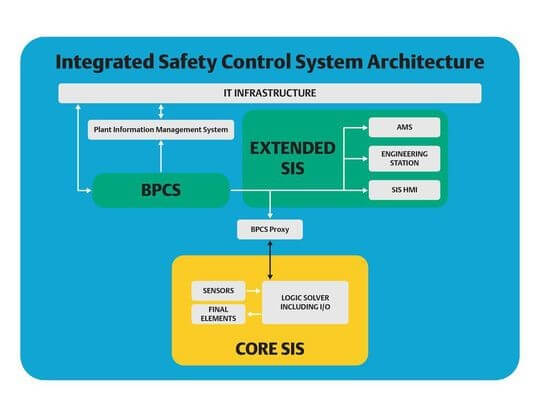
Creating a safe and secure automation process starts with implementing a well-designed basic process control system (BPCS) and safety instrumented system (SIS). Government agencies and industry associations offer guidelines and requirements for how these systems should be connected and separated—most importantly with the requirement that the SIS and BPCS should be logically independent regardless of the level of physical linkage—but organizations still need to choose an architecture that falls within those guidelines.
Emerson’s Alexandre Peixoto and Sergio Diaz recently published an article in in Process Worldwide explaining how integrated control and safety systems (ICSS) provide the ideal solution for many organizations by combining logical separation with physical hardware connectivity.
Cybersecurity
One of the core concerns when choosing an automation system architecture is to create preventive and mitigating layers of defense around the systems.
Multiple layers of protection bolster the strength against unauthorized access…Architectures use layers of defense that best suit their needs and deter potential risks. And to varying degrees, layers for each architecture assist or detract from the daily task of process control.
Of the three main styles of SIS and BPCS architecture—separate, interfaced, and integrated— integrated systems provide the easiest architecture for creating layers of defense. Because the systems are physically integrated but logically separated, the organization does not need to duplicate all cybersecurity protections on both the SIS and BPCS.
The defense-in-depth layers around the BPCS in an ICSS configuration supplement
dedicated cyber-protection layers for the SIS. The SIS still has its own specific cybersecurity features such as the logic solver lock functionality.
Lifecycle Maintenance
Automation systems are not set-and-forget. Over the years they will need patches and updates to stay as secure and productive as possible. In addition, processes and equipment will likely change over the decades that automation systems are expected to operate.
A fully integrated control and safety system can be easier to maintain over the lifecycle of the systems because the SIS is wrapped in layers of defense, many of which also defend the BPCS… In addition to the ease in layers of defense, integrated diagnostics provide lifecycle maintenance simplicity.
Having a single, integrated system also reduces the number of potential weak links in the system. Engineered connections in interfaced systems often use open protocols which—if engineered improperly—can
ultimately increase potential points of failure or increase cybersecurity vulnerabilities.
With an integrated architecture, there are typically mechanisms in place to automatically prevent the introduction of additional risk. In fact, systems such as the DeltaV™ DCS and SIS
can detect the source of changes, detect corruption in packets, and automatically perform some validation on data moving from BPCS to SIS (and vice versa) to ensure changes are authentic.
To learn more about the benefits of ICSS architecture for your industry, visit Emerson’s DeltaV SIS Integration page, or you can discuss the benefits and drawbacks of different automation architectures with industry experts in the Emerson Exchange 365 community.


