As analytics continues to turn the vast and growing sea of digital data into useful information, the need for strong cybersecurity also grows. In a CIO Applications article, Addressing the Complex Cyber Security Needs of Digital Manufacturing, Emerson’s Bob Karschnia highlights the collaboration between suppliers and end users to maintain an effective defensive cybersecurity strategy.
 Bob opens noting points of vulnerability where industrial wireless networks connect into wired systems. Security considerations must include an end-to-end holistic view of these data handoff points. He explains that security may be applied differently by different suppliers and ultimate responsibility:
Bob opens noting points of vulnerability where industrial wireless networks connect into wired systems. Security considerations must include an end-to-end holistic view of these data handoff points. He explains that security may be applied differently by different suppliers and ultimate responsibility:
…falls to the network managers to review specifications and practices carefully as they implement digital manufacturing projects.
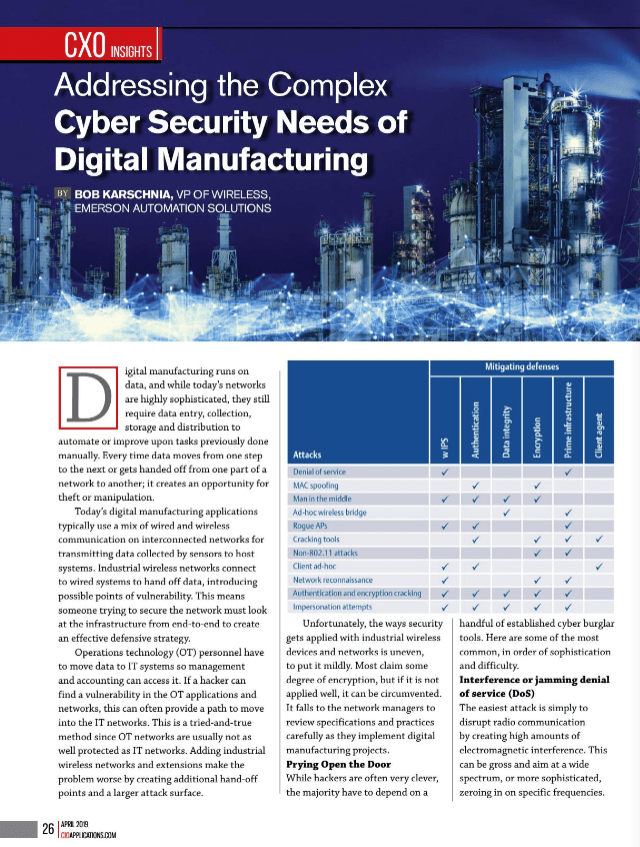
He highlights the common cybersecurity attack vectors:
- Interference or jamming denial of service (DoS)
- Bad data DoS
- Ad-hoc wireless bridges
- Rogue APs [access points]
- Man in the middle
- Reconnaissance and cracking
Cyber defenses should include strategies for access control, network protection through encryption, preserving data confidentiality and integrity, and integrating a solution. This is not a comprehensive list of defenses, but ones that can help address the common attack vectors.
Read the article for more on each of these attack vectors and defensive measures for addressing them.
Visit the Cybersecurity Services section on Emerson.com for more on the strategies, tools and services to help you maintain a robust cybersecurity poster over the life of your manufacturing and production operations. You can also connect and interact with other cybersecurity experts in the Services group in the Emerson Exchange 365 community.

