Safety instrumented systems (SIS), which are designed to take the process to a safe state in trip conditions, come in several architectures with the basic process control system (BPCS). The SIS and BPCS can be totally separate, interfaced or integrated, yet separate. While the debate on which approach is best has been going on for a long time, what are they cybersecurity considerations of these architecture choices?
 In a Control Engineering article, Sustainable cybersecurity architecture for safety instrumented systems, Emerson’s Sergio Diaz and Alexandre Peixoto explore these considerations.
In a Control Engineering article, Sustainable cybersecurity architecture for safety instrumented systems, Emerson’s Sergio Diaz and Alexandre Peixoto explore these considerations.
They open noting that all architectures can be made more cyber-secure.
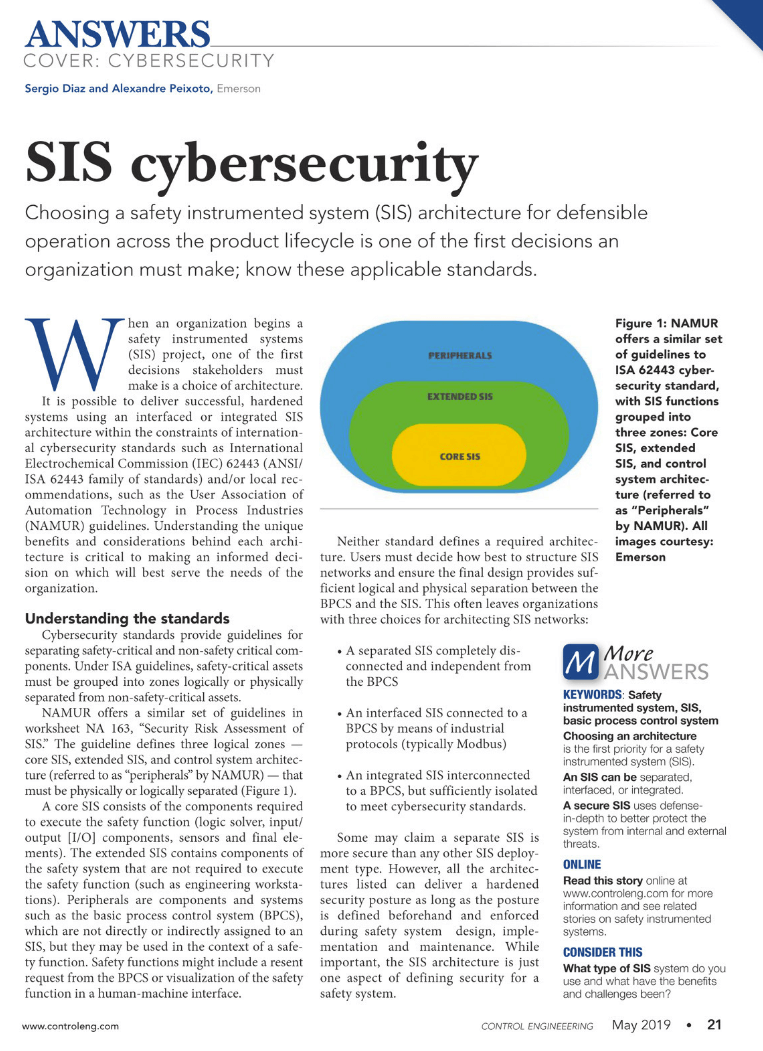
It is possible to deliver successful, hardened systems using an interfaced or integrated SIS architecture within the constraints of international cybersecurity standards such as International Electrochemical Commission (IEC) 62443 (ANSI/ISA 62443 family of standards) and/or local recommendations, such as the User Association of Automation Technology in Process Industries (NAMUR) guidelines.
They describe 3 zones—Core SIS, Extended SIS, Peripherals (control system architecture)—in the NAMUR guidelines. These are similar guidelines to the ISA 62443 standard.
A core SIS consists of the components required to execute the safety function (logic solver, input/output [I/O] components, sensors and final elements). The extended SIS contains components of the safety system that are not required to execute the safety function (such as engineering workstations). Peripherals are components and systems such as the basic process control system (BPCS), which are not directly or indirectly assigned to an SIS, but they may be used in the context of a safety function.
One of the key concepts in cybersecurity is defense in depth where the entry points into a system have defenses at multiple levels against unauthorized access. For separate SIS and BPCS architectures this means maintaining an “air gap” between systems with no connections between them. A challenge with this architecture is access to the SIS:
…for tasks such as extracting event records for sequence of event analysis, bypasses, overrides, proof test records or performing configuration changes and applying security updates. USB drives, which are often used to implement these updates, are not easy to protect.
From a defense-in-depth standpoint, this separate architecture:
…leaves users managing two separate sets of defense-in-depth architectures. This creates a high potential for more work hours, longer downtimes, and additional areas where oversights might leave holes in the protection layers.
Similarly, an interfaced BPCS and SIS thought a common industrial protocol such as Modbus require the management of multiple defense-in-depth approaches for each system plus the communications path between them. This architecture does minimize the need for USB or other physical data transport devices.
The integrated system approach minimizes the number of entry points that need secure defense-in-depth strategies.
Read the article for much more on these considerations to maintain a defensible and cyber-secure BPCS and SIS throughout their lifecycle.
Visit the Safety Instrumented Systems section on Emerson.com for more on the integrated SIS approach in DeltaV SIS, Ovation SIS as well as the separate or interfaced approach with a standalone SIS. You can also connect and interact with other functional safety experts in the Control & Safety Systems group in the Emerson Exchange 365 community.


