Emerson’s Nick Janouskovec presented NERC CIP-015-1 Internal Network Security Monitoring and Power and Water Cyber Security Network Security Monitoring at the 2025 Ovation Users’ Group Conference. His presentation provided a brief history of NERC CIP [North American Electric Reliability Corporation Critical Infrastructure Protection], a network security monitoring (NSM) overview, mapping leading NSMs to NERC CIP requirements, and how NSMs are in the Ovation distributed control system architecture.
Nick opened by sharing a brief history of NERC CIP. NERC was founded in 1968 as a voluntary organization, formed directly as a result of the extensive blackout in the Northeast U.S. It:
… was formed to address the obvious reliability issues stemming from the 1965 blackout and the much greater utility interdependence that resulted from further grid integration, while maintaining responsibility for reliability within the industry itself, where operational and planning expertise reside.
The organization gained momentum as the popularity of the internet grew in the early 2000s and with the advent of the 2005 Energy Policy Act. It made an agreement with Canada’s National Energy Board for the provinces of Ontario, Quebec, and Nova Scotia. In 2007, the first reliability-related standards were passed and made enforceable.
Part of the NERC CIP standards includes the need for Network Security Monitoring (NSM). These applications are designed to monitor network traffic to detect malicious activity. This solution is broader than IDS (Intrusion Detection System) or NID (Network Intrusion Detection).
The Dragos NSM solution maps to the following NERC CIP standards:
- CIP-002 – Bulk electric system (BES) Cyber System Categorization. Passive monitoring techniques to observe and identify devices connected to the network
- CIP-005 – Electronic Security Perimeter(s) (ESP).
- Monitor within and outside ESP
- Identify external communications unrouted via extensible authentication protocol (EAP)
- Identify remote access sessions
- CIP-007 – Systems Security Management. Log events and generate alerts detecting malicious code, successful, and failed login attempts
- CIP-008 – Incident Reporting and Response Planning. Provides robust detection capabilities, centralized management, automated response, and forensic analysis tools
- CIP-010 – Configuration Change Management and Vulnerability Assessments.
- Develop baseline configurations for devices
- Passive vulnerability assessments.
- CIP-012 – Communications between Control Centers. Identify unencrypted communication protocols in use if the responsible entity is utilizing encryption between control centers
- CIP-015 – Internal Network Security Monitoring.
- Develop baseline configurations of network traffic
- The Baseline feature detects deviations in assets
- Passive monitoring to detect anomalous network activity and identify assets
- Detect and alert on threat behaviors
Here’s how the Nozomi Networks NSM maps to NERC CIP:
- CIP-002 – BES Cyber System Categorization. Categorize inventory, understand, and analyze assets and risk indicators
- CIP-003 – Security Management Controls. Centralize network visibility, provide security access management, analyze communications and protocols
- CIP-004 – Personnel & Training. Create custom CIP reports, dashboards, and queries for training materials
- CIP-005 – Electronic Security Perimeter(s). Detect unauthorized network access, use of cleartext passwords, and unencrypted remote access, and manage assets based on uniquely assigned electronic security perimeters
- CIP-007 – System Security Management. Monitor traffic specific to ports, switches, and control networks. Track BES assets
- CIP-008 – Incident Reporting and Response Planning. Monitor events and centrally manage network monitoring, consolidate and correlate events and alerts, report events and incidents, and remediate with leading incident response partnerships and integrations
- CIP-010 – Configuration Change Management and Vulnerability Assessments. Monitor baseline configurations with change notifications and alerts for change and version control, reviewing relevant vulnerabilities
- CIP-013 – Supply Chain Risk Management. Utilize deep packet inspection of industrial protocols to perform configuration management on assets and devices, monitoring and reporting vulnerabilities, security events, and incidents
- CIP-015 – Network Security Monitoring within the trusted zone. As a continuous internal monitoring solution, the sensors instantly detect all connected assets and use artificial intelligence trained on the environment to determine baseline behavior and recognize anomalies thereafter.
Dragos
For NERC CIP-015-1, Dragos implements processes for internal network security monitoring (INSM) of networks protected by the electronic security perimeters of high-impact BES cyber systems and medium-impact cyber systems with external routable connectivity, providing methods for detecting and evaluating anomalous activity.
It implements these processes using a risk-based rationale with network data feeds to monitor activity, using:
- OT-native passive network monitoring with Dragos Sensors
- Edge-compute-enabled east–west monitoring
- Single- and multi-sensor threat analytics across trusted zones
- Active collection to enrich asset inventory and context
It detects anomalous network activity through:
- Intelligence-driven detections with OT context produce high-confidence alerts
-
- Anomaly-Based Detections
- Modeling Detections
- Configuration Detections
- Intelligence-Driven Detections
- Threat Behavioral Detections (e.g., TTPs)
- Indicators/IoC Detections (IoCs)
- Anomaly-Based Detections
-
The Dragos NSM evaluates anomalous network activity detected by:
- Panel displays four threat detection types for triage
- Raw historical evidence supports deep investigation
- Query Query-focused datasets (QFDs) enable structured, retrospective analysis
- Expert-authored playbooks and case management guides provide consistent evaluation
- Integrated ICS/OT threat intelligence adds context and informs escalation
It retains INSM data associated with anomalous network activity by:
- Collecting and storing network activity data feeds in support of R1 is a core capability of the Platform
- Indefinite retention for cases opened in the Platform and all associated evidence
- Dataset sizing and associated online/offline storage retention are expandable
- Backup and restore capabilities ensure subject data is retained, recoverable, and available for audit and investigation
The Dragos solution protects INSM data collected in support of R1 and data retained in support of R2 to mitigate the risks of unauthorized deletion or modification by:
- System configuration details are available, including centralized audit logging
- Multi-Factor Authentication (MFA)
- Data retention controls are actively enforced, with records verifying the last successful backup
- Ability to backup to external locations to ensure redundancy
- Indefinite retention for cases opened in the Platform and all associated evidence
Nozomi
Nozomi addresses the NERC CIP-015-1 requirement, documenting INSM processes. Nozomi sensors instantly detect all connected assets and their associated intelligence to determine baseline behavior and identify anomalies thereafter. During implementation, the system can also be configured based on best practices across hundreds of similar environments to minimize false positives.
It identifies network data collection locations and methods through the deployment of sensors, which can be documented to be presented in the analysis conducted before installation. Inventory of the sensors, network drawings, and asset inventory will assist in evidence recollection.
Sensors will detect anomalous network activity. Baseline of learned assets may be presented to contrast against anomalies shown as alerts. It also provides historical alert data.
Network graphs, asset and network information, alerts (including timelines and details), forensic comparisons of baselines, and playbooks (including relevant methods, responses, and escalation processes) provide the method to evaluate the detected activity.
To address the requirement to document processes to protect the data collected, the Nozomi platform offers adjustable retention settings and images of the sensor, including all data, which can be backed up to a desired location. Backups and exports of the data can be stored and encrypted in the NAS.
Finally, the Nozomi platform provides the relevant system configuration details and reports to inform the required documentation, which satisfies the requirement to document processes for retaining network communications data and other metadata collected for analysis.
Conclusion
CIP-015-1 will go into effect for High Impact and Medium Impact Control Centers and backup Control Centers with ERC on October 1, 2028. All other Medium Impact BES Cyber Systems with ERC will be required to comply by October 1, 2030. It’s essential to act now to assess your network and these NSM solutions, and reach out to Emerson’s Ovation team for assistance in moving this effort forward, since selecting, architecting, and building a program around NSM will take time.
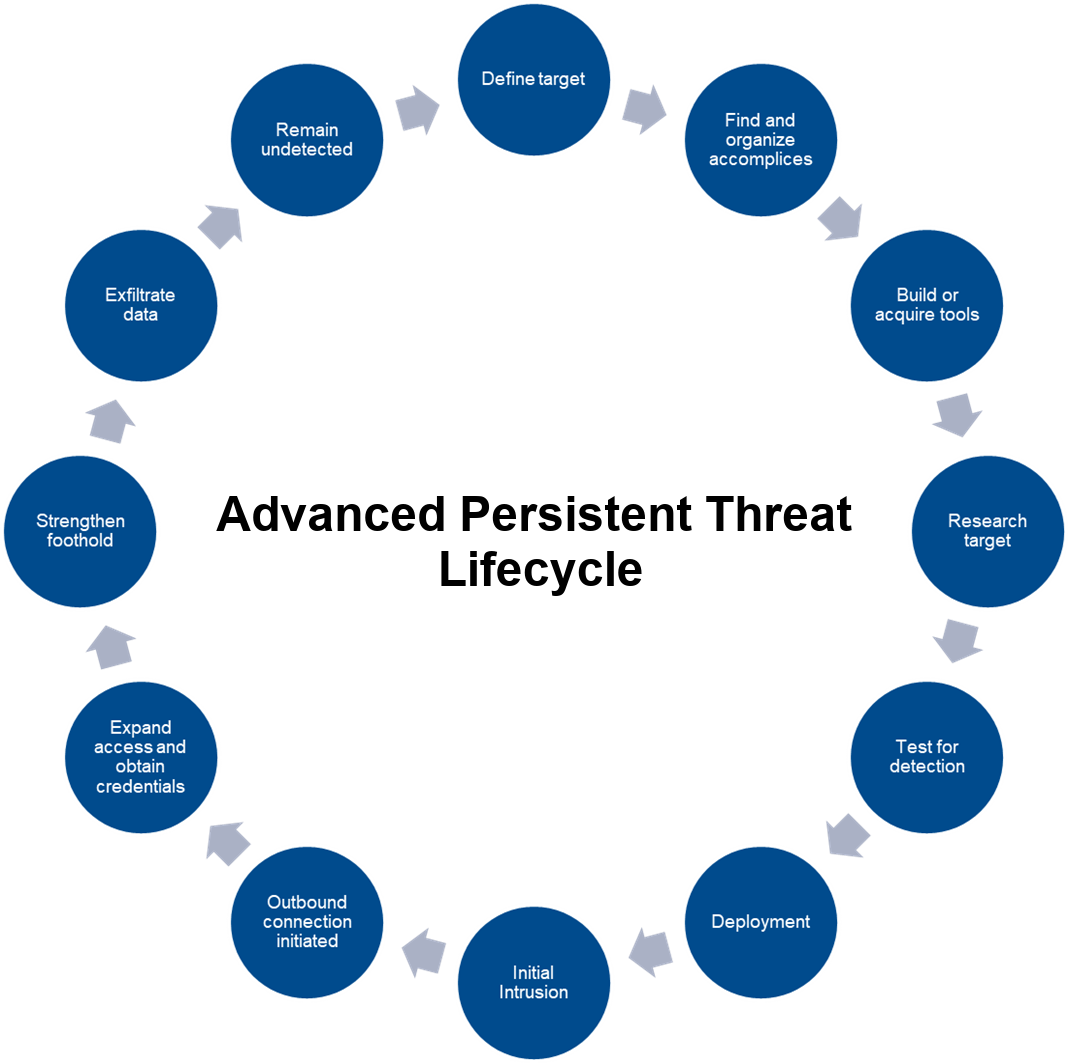
Network Security Monitoring is one of, if not the best, protections against Advanced Persistent Threats (APTs), and everyone should utilize NSM, even if CIP-015-1 does not apply to them. Emerson works closely with these two leading NSM providers.
Visit the Ovation Advanced Cybersecurity Suite Services page on Emerson.com for more on the resources and expertise available to assist in your NERC CIP compliance efforts.