Cybersecurity remains a top concern for process manufacturers around the globe. This is due to the fact that threats are increasing, automation and IT staffs are demanding comprehensive security, regulations and standards are emerging, and proactive measures are being required to meet increasing threats.
I mention this for the DeltaV users joining us at the Emerson Exchange conference next week in the Dallas/Fort Worth Texas area. You’ll want to schedule session 4-4662 Protecting DeltaV from Cyber Attacks using OPC .NET. The presenters, Emerson’s Lee Neitzel and Bob Huba will share how this technology and the security requirements of the plant come together to increase security robustness.
Here’s the abstract of their presentation:
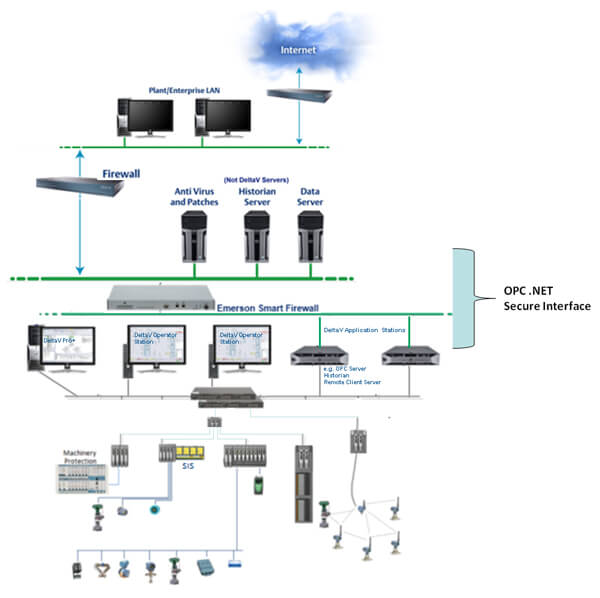
Protecting a DeltaV system from cyber attacks is accomplished through a defense-in-depth strategy composed of a combination of security features and processes that are compliant with emerging industrial security standards. One element of this strategy, OPC .NET, is described along with how to use it effectively at the site.
The session will be Tuesday October 1 at 1:00pm in Ft Worth 6 and repeated Thursday, October 3 at 2:15om San Antonio 6 in the Gaylord Texan Hotel.
Security requirements for the automation system must take into account that each plant has its own security requirements. The DeltaV system often must integrate with plant and corporate IT security. These plants do not go through security certification conducted by 3rd parties as NERC Critical Infrastructure Protection (CIP) does for the Power industry. Technologies and services provided by Emerson play a role in these overall security requirements.
Lee and Bob share some of the global activities including the U.S. NIST Cybersecurity Framework from the Executive Order — Improving Critical Infrastructure Cybersecurity as well as the WIB vendor security certification process from the International Instrument Users Association. Three aspects of the WIB requirements include lifecycle, defense in depth, and maturity model on a path to best practices.
For example, defense in depth for a control system includes antivirus protection, operating system security patching, and software hotfixes at the lowest level. User access control and workstation hardening (ex. disabling USB ports) is at the next level. Out a level further is a secure network architecture design, network lockdown capability, secure remote access, firewalls, and security policies. Finally, at the top layer is physical security to access the system.
They explore these levels in greater depth and share how various technologies fit in. How OPC .NET fits in is that it was developed to address security issues in OPC Classic, developed back in the 1995-1996 timeframe. Security issues include DCOM with its firewall ports, configuration complexity, difficulty in callback authentication, complex proxy installation, and program registration complexity.
It was created as an independent thin wrapper to wrap any OPC server and allow OPC clients, using OPC .NET client wrappers, to talk through OPC .NET. The base encryption and authentication is provided by the .NET Windows Communications Foundation (WCF). Base user privileges are defined by access control lists and require the user identity to be maintained.
OPC .NET addresses shortcomings in OPC Classic such as robustness through automatic recovery from connection failures and loss of client configuration. It uses the HTTP and TCP open ports through the firewall instead of opening additional ones.
You’ll want to catch one of the sessions and bring your questions for Lee and Bob during the exhibit hours of the conference.