Panelists at a session at the 2019 ARC Industry Forum, Safety Systems: Integrated versus Not? Does It Really Matter?, set out to discuss the pros and cons of the approaches and how they accommodate different risk factors.
ARC Advisory Group’s Mark Sen Gupta moderated this panel which included executives from Air Products & Chemicals, Dow Chemical, Chevron Energy Technology, and exida. Mark covers the process safety space for ARC. He opened by defining integrated safety as the control and safety sharing common software and/or hardware.
There is an ideological conflict between those thinking that the integrated or the non-integrated system is the only way to go. For integrated systems, the safety system can be used independently with other suppliers’ control systems.
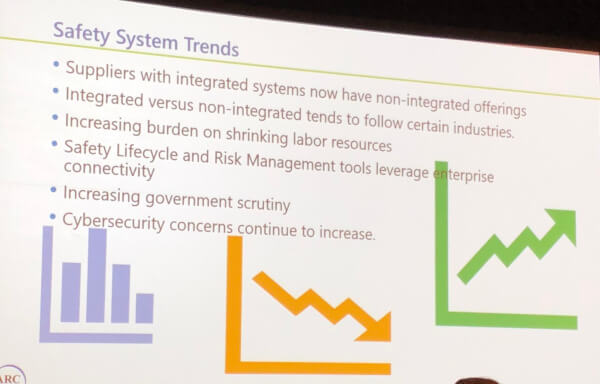
Mark shared some trends in safety systems:
With these introductory remarks, Mark invited the executives up for a question and answer session. The panelists have a mix of non-integrated and integrated safety and basic process control systems (BPCS).
 Chris O’Brien with exida noted that there is not one way. Different systems designs can meet the risk mitigation requirements that the safety systems are designed for. A question came in about cybersecurity and safety systems and whether integrated or segregated systems were better. One of the manufacturers on the panel noted that in either type of architecture, strong cybersecurity processes and technologies are required. Questions need to be asked about where the data is needed, how is it to be used, and how should they systems be architected to address these needs yet maintain a robust cybersecurity footing.
Chris O’Brien with exida noted that there is not one way. Different systems designs can meet the risk mitigation requirements that the safety systems are designed for. A question came in about cybersecurity and safety systems and whether integrated or segregated systems were better. One of the manufacturers on the panel noted that in either type of architecture, strong cybersecurity processes and technologies are required. Questions need to be asked about where the data is needed, how is it to be used, and how should they systems be architected to address these needs yet maintain a robust cybersecurity footing.
Risk mitigation from a cybersecurity standpoint should be put into the design and work processes and managed throughout the lifecycle. There is no panacea for a single design that will make everything cyber-secure. Much like safety, it’s managing and mitigating risks from the lowest to the highest levels of the safety and control architecture.
Communications stacks often come from 3rd parties which can be common to both the control & safety systems. IEC 62443 defines coding standards to avoid these potentially common points of vulnerability.
Another question came in on a hypothetical if one has a greenfield project, what would the members of the panel recommend between integrated and non-integrated control & safety systems. Considerations include I/O counts of the process, the needs for similar data between systems. In some cases, the safety system may need to act on machinery health information in the BPCS where an integrated approach works better. In some cases, just a few loops need a safety instrumented function and there is no need to share information from these with the BPCS.
One questioner was a proponent of interfaced but not integrated and wondered if any of the panelists used data diodes or other technologies to guarantee no flow back of data to the safety systems. One of the panelists noted that they have piloted the use of data diodes, but they were weighing the amount of risk reduction versus the added complexity and costs to implement. Another consideration is what the operators need to see from each system including diagnostic information. The global IEC 61508 safety system is a performance-based, not prescriptive-based standard, that does not require a certain approach. Each application has different risks to analyze and mitigate.
A questioner asked what is the impact of digitalization on cybersecurity and safety. A panelist noted that their approach is to take one step at a time and deal with digital transformation levels at the BPCS side first. There are enough considerations there to sort through to not add safety systems into the scope. Another panelist noted they ask the question, “Does a safety instrumented function need access to the information required to perform the function?” If so, there needs to be a comprehensive look at access control, the validity of the information, the security of information transmission, etc. Right now, no one is using wireless devices in their safety instrumented functions because safety is all about being risk adverse and not ready to embrace this technology that was introduced for monitoring and certain regulatory control applications.