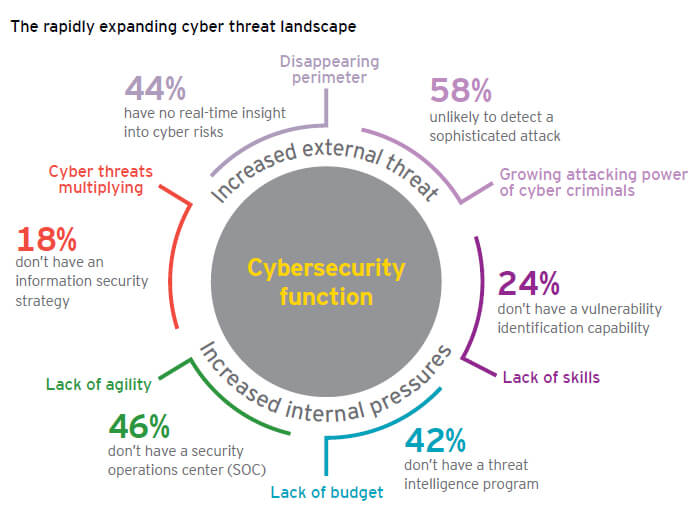
In the past, we discussed how the metals and mining industry was increasingly becoming a target for cyber-attacks. An Ernst and Young report, Business risks facing mining and metals 2015–2016 recently upgraded cybersecurity into its top 10 business risks—up two spots to number nine.
In this report, a 2014 Global Information Security Survey indicated that 65% of mining and metals companies responded that they had experienced an increase in cyber threats over the past 12 months. Despite this threat increase, the survey results showed that only 47% of the respondents planned to increase their organization’s total information security budget in the next 12 months, highlighting a gap in readiness to mitigate these risks.
Source: Ernst & Young – Business risks in mining and metals 2015-2016
The report mentions three major reasons for this increase in cyber threats:
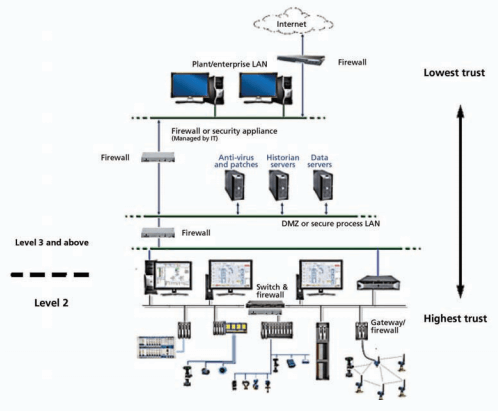
- Convergence of operational technology: One of the vulnerabilities that the mining and metals sector faces is derived from the convergence of IT and operational technology (OT) and the increased cyber risk that it creates. Advancements in big data, mobile computing and the “internet of things” have enabled exciting opportunities in OT to improve safety, sustainability and productivity. However, at the same time, they have exposed mining and metals businesses of all sizes to increased threats of cyber hacking.
- Historic underinvestment and current budget trends: Mining and metals organizations have historically underinvested in security, and security budgets are often static, despite increasing cyber threats. With total budgets remaining flat in recent years, competing priorities and budget constraints mean mining and metals companies are addressing only the top one or two priority areas each year.
- An understanding of whether the organization has been breached: There is a growing body of evidence suggesting the majority of large organizations have been breached and either have threat actors operating undetected within their environments or have failed to identify the breach when it occurred.
This report highlights that cybersecurity should be a focus of the metals and mining industry. We have seen in the news the damage these cyber-attacks can cause to the reputation and productivity of a company. While companies try to do cost-benefit analysis when they are analyzing investment options, especially now in an economic down turn, I believe that it will be more costly to deal with the consequences of a breach than to invest in mitigating the risk.
This was highlighted in a Wall Street Journal article, Companies Wrestle With the Cost of Cybersecurity, which noted, “Analyst Aviva Litany estimated for every $5.62 businesses spend after a breach, they could spend $1 beforehand on encryption and network protection to prevent intrusions and minimize damage.”
Some people might think that metals and mining sites are not affected because they are in remote locations and attackers would not reach them because they have limited contact with the outside world. As we have seen in the news, these attacks have penetrated all kind companies regardless of their location or cybersecurity system. They have even penetrated federal governments including the United States that should have leading cyber-security systems and processes. Many industrial sites, including metals and mining sites, with less sophisticated security system are at risk for these attacks.
Specifically in process control, an area that has a direct impact in production, not enough is being done or what is done is the extreme of cutting the control system from any network and internet access. By closing access to everyone, we are limiting access to vital information for other departments and remote expertise and sometimes leaving the rest of the organization in the dark about real-time production information.
Total disconnection also affects remote services that suppliers are able to offer in order to help miners remotely troubleshoot equipment and/or production issues. Too little access also affects the productivity of the company because in today’s environment process control information and remote support is critical for faster and more efficient planning. Also, troubleshooting problems with the help of a remote expert and formulating Key Performance Indicators (KPIs) in real time may be removed.
That is why I think we need to find the balance between connectivity and security, and we can start by following the six steps derived from converging ISA/IEC/WIB standards. These steps are greatly detailed in this InTech magazine article, Six steps to control system cybersecurity. These steps reinforce the concept that security cannot be accomplished just by buying a control system with the right security features.
The author emphasizes that security is just as much an ongoing process as it is technology. These steps can be implemented in an evolutionary fashion so that security improves over time. A maturity model specified in the IEC standard defines the evolution of security. It should encourage automation professionals to start down the path to improved security, rather than thinking security is just too ominous and complicated to address.
As miners continue to digitize all aspects of their production, they will gain more benefits, but they will have to embed cyber security processes and technologies in all their initiatives. It is a tough balancing act to secure your networks yet grant access to vital information, but miners will need to give these challenges the priority they require.