Recent world events—from the expansion of remote access in response to COVID restrictions to high-profile industrial cyberattacks—have put a renewed focus on cybersecurity. While cybersecurity needs vary from organization to organization, there are common, critical steps every company can follow to improve their cybersecurity posture. Alexandre Peixoto and Lee Neitzel explore five of these strategies in automation.com’s May Connectivity and Cybersecurity eNewsletter.
Most cybersecurity experts offering their services to industrial users suggest two steps when launching a program. First, perform a risk assessment. Second, follow appropriate cybersecurity standards to guide design of your security strategy. Both are important, but they are major undertakings and their effectiveness depends on how they are done and who does them. Instead of focusing exclusively on these strategies,
A more practical approach is to recognize the primary objective of cybersecurity is to reduce the chance threats will succeed and disrupt or compromise the system. This approach starts by identifying how threats enter a control system and how they work their way through it to their end targets, and then placing defensive measures in the appropriate places. While there are many possible threats, malicious code injection and user interface attacks are the most likely to occur and cause harm.
The article suggests five areas that users can address now, with simple strategies to make it more difficult for an intruder to get in and navigate around inside your networks. They are:
- Establish a security perimeter
- Protect exposed interfaces
- Decouple ICS and business systems
- Minimize use of operating system administrator accounts, and
- Log critical user activities.
Let’s take a closer look at number four to give you a preview. This point is important because hackers always want their malicious code to run under an administrator account so it can create new users and make all sorts of other changes in the system.
Non-administrative users, including engineers and operators, and software services (software applications that run in the background without a user interface) should be assigned to their own restricted operating system accounts, and should never be assigned as members of administrator groups/accounts. In addition, keeping network administrator accounts separate from operating system accounts prevents attackers who have breached a workstation or server from gaining access to the network administrator account and removing network device firewall rules.
These five points are not an exhaustive list by any means, but they’re a good place to start, and implementing each one can go a long way toward protecting your networks. Training people and avoiding attacks via social engineering are also very important. Many additional strategies will be added to the list during a more comprehensive evaluation program.
Cyber threats will always evolve, and attackers will constantly develop new strategies. Cybersecurity is an ongoing conflict and both sides are working to improve their methods, good and bad. By focusing on establishing strong defense-in-depth strategies to secure your systems, you can build a strong, scalable foundation to drive better security today and into the future, so you are ready for new threats as they emerge.
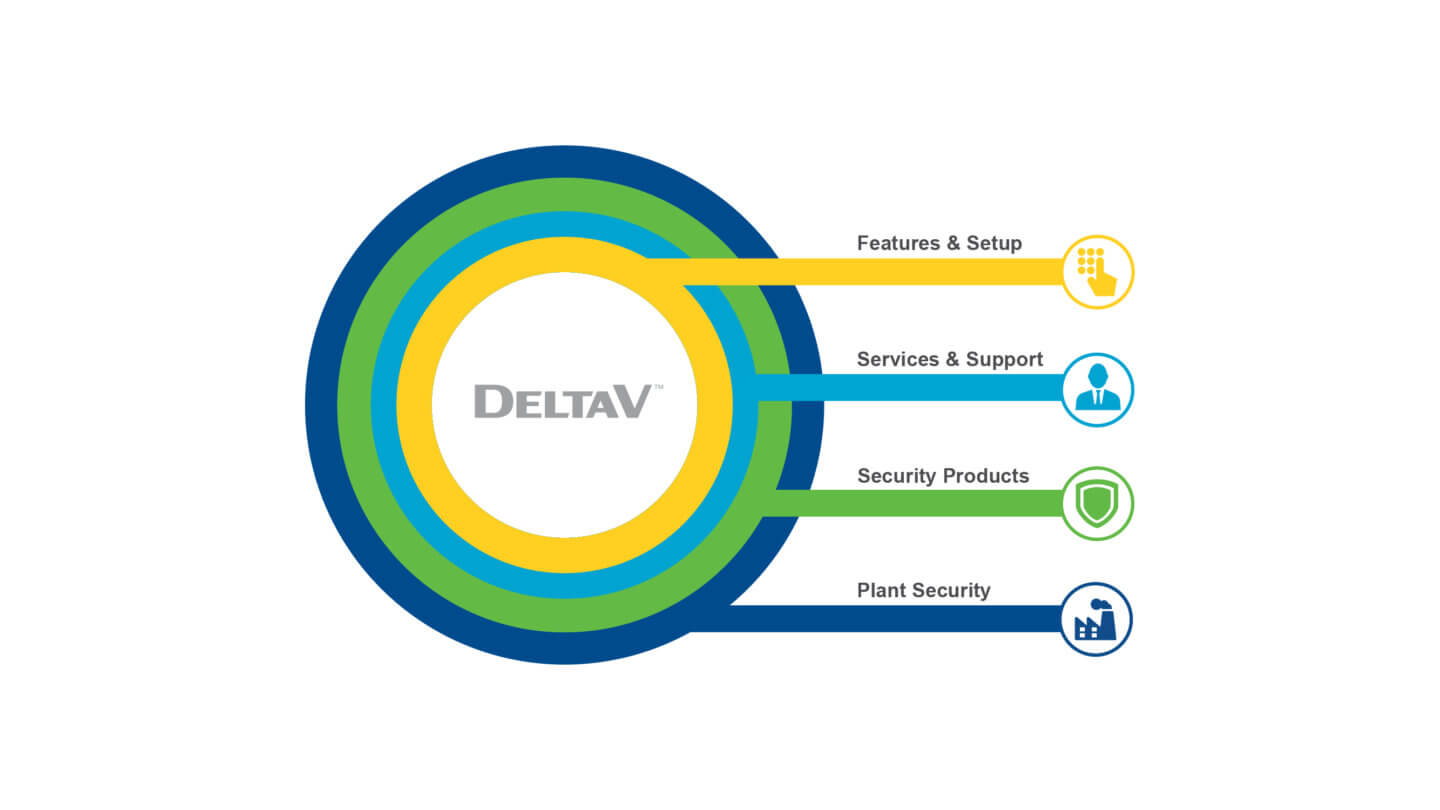
Visit Emerson’s DeltaV Cybersecurity pages at emerson.com. Emerson’s cybersecurity services are designed to help you identify vulnerabilities, close protection gaps, and secure your process control systems from cybersecurity risks before an attack threatens to impact your business.
You can also connect and interact with other engineers in the Oil & Gas, Chemical, and Life Science Groups at the Emerson Exchange 365 community.

